
By Larry Magid
This post first appeared in the San Jose Mercury News
The Black Hat security conference is sometimes viewed as a “hacker’s” convention, but most of the people in attendance are security professionals and researchers from companies, academia and government.
Microsoft, Symantec, Trend Micro and other security companies are well represented. But some of the security researchers at the annual conference, which I attended this week in Las Vegas, might also happily consider themselves “hackers” because that’s basically what they do.
For example, one workshop had been scheduled to show how it’s possible to hack into implanted medical devices like pacemakers, defibrillators and insulin pumps, potentially remotely killing the victim. But in a sad irony, the person scheduled to give that talk, 35-year-old security researcher Barnaby Jack, was found dead in San Francisco a few days before the conference from unknown causes, though foul-play is not suspected. Jack was an example of someone who hacked for the greater good. He was memorialized at the opening of the event and the session he was supposed to present at was turned into a celebration of his life.
But there remained plenty of hacks at Black Hat.
- I attended a presentation where a group of researchers showed how they could use a rogue cell phone charger to inject malware called Mactans into current generation iPhones and iPads.
- Another briefing showed how to break into a home security system by intercepting signals before they can alert authorities.
- Another showed how you can use a femtocell (common devices used to improve cell phone reception in weak areas) to clone or spy on someone else’s cell phone. There also was a workshop on how to exploit Oracle’s Java language — hardly big news since we frequently hear about Java hacks.
- Another presentation, titled “Android: One Root to Own them All,” promised to reveal how to break into a “wide number of Android devices.” Apple’s iOS is also subject to exploits, but because Google doesn’t vet apps on its Google Play store, it’s easier for malicious software to find its way onto Android phones.

The vulnerability of mobile devices was a major topic, which makes sense considering the explosion in smartphones and tablets — all of which communicate wirelessly by cellular networks, Wi-Fi, Bluetooth, Near Field Communication (NFC) or some combination of all of them. One workshop focused on spy software that “gathers information such as text messages (SMS), geo-location information, emails and even surround-recordings.” The presenters offered a “novel proof-of-concept attack technique” to bypass traditional mobile malware detection measures.
I’m not particularly paranoid when it comes to the security of my own wireless devices, but upon arriving at Black Hat, I was warned that the slogan “What happens in Vegas stays in Vegas” doesn’t apply to mobile data when there are thousands of hackers in town. The organizers of the conference sent visiting press a rather ominous warning to be very, very careful. I was warned that my “hotel key card can be scanned by touch, so keep it keep in your wallet,” and was told not to use ATM machines or Wi-Fi networks near the conference. At one point, when I logged into my own MiFi wireless hotspot I noticed that I suddenly had two hotspots. One was my regular encrypted hotpot but there was an unencrypted one with the same unique name, likely set up by a hacker to trick me into logging in.
NSA Director get mixed reception
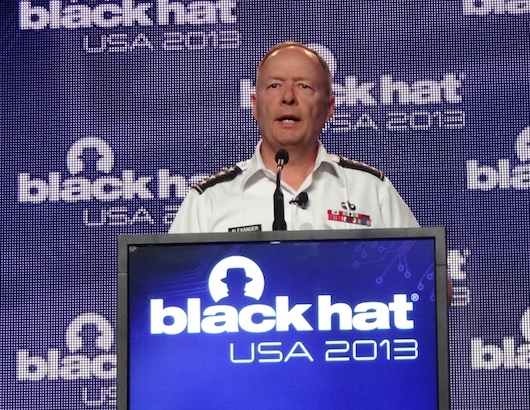
Probably the most anticipated presentation came from a guy who runs an organization that has recently been accused of hacking. His name is General Keith Alexander and he’s director of the National Security Agency.
As you might expect, he used his time at the podium to justify the NSA’s surveillance programs, arguing that before 9-11 “we failed to connect the dots.” He said that the current programs used by NSA are legal, authorized, overseen by all three branches of government and audited. “We have tremendous oversight and compliance in these programs,” he said.
Alexander said that even if he wanted to, he couldn’t use NSA resources to read the email from his four kids. Any access, he said, is audited to make sure that the person looking at the information had a legitimate reason.
The crowed was mostly polite but there were some hecklers, including one person who shouted out that Alexander “lied to Congress.” After the presentation, I spoke to a number of delegates, and many questioned whether he was telling the truth. I’m in no position to know one way or the other, and I’d like to believe that he, President Obama and the other officials who have weighed in on these surveillance issues are completely truthful.
But just hours before the General’s speech, the Guardian newspaper published even more serious allegations of NSA snooping based on reports from Edward Snowden. If Snowden is lying, that would be unfortunate. But Alexander and other public officials are lying, it borders on tragic.